OpenVPN on Dedicated Wireless Access Point (VAP)
From DD-WRT Wiki
Contents |
[edit] DISCLAIMER
Please note that this wiki is outdated and not applicable in current releases of DD-WRT. Please consult the OpenVPN guides on the forum as they are more up-to-date until this wiki has been updated accordingly. Thanks.
[edit] Introduction
This guide will walk you through the steps required to set up a Virtual Access Point (VAP) that is funneled through an OpenVPN tunnel, while the main access point is pushed through your normal WAN link provided by your ISP. I will link to other sections of the Wiki where possible.
This guide was written with OpenVPN in mind, but it should work just as well for a PPTP tunnel. Provided that the GUI implementation of PPTP doesnt redirect your gateway through the tunnel, and PPTP in your version of DD-WRT functions.
Note: This procedure was tested on an ASUS RT-N16 running DD-WRT v24-sp2 (12/08/11) big (SVN revision 17990M NEWD-2 K2.6 Eko) I have not tested this with PPTP. If you get it running, please PM Vespian in the forums and let me know how it worked out for you so I can edit this guide.
I was not successful in getting to work with OpenVPN on builds past 18946. TLS Auth fails to negotiate properly.
[edit] Set up OpenVPN
You will need to set up your VPN. I am not going to rewrite the entire guide on how to accomplish that, as it can be found here (for username/password auth) or here(for PKI).
Just a few things to make sure of here besides the default setup.
1. ENSURE that redirect-gateway def1 is NOT set in your additional config dialog. We need to define our own routes later.
2. ENSURE that route no-pull is NOT set in your additional config dialog. (This will allow OpenVPN to set up the basic routing and iptables rules that you will need)
Also, take note that TUN interfaces are for routing, and TAP interfaces are for bridging. The following instructions are built around a TUN interface being set up by OpenVPN. If you have a TAP interface the instructions below will not work for you. Under most circumstances you will not need the features of a bridged TAP connection.
If you need to use a TAP connection, set up is fairly simple. Follow these instructions until you get to the point where you assign wl0.1 to br1... and put the TAP interface created by OpenVPN on the same bridge as wl0.1... and you're done.
IMPORTANT: Make sure your VPN connects before moving on with this guide. You can verify connection in the Status -> OpenVPN tab. It will say STATUS: CONNECTED.
[edit] Create and Configure Your VAP.
Go to your wireless tab and on the bottom of the page hit the "Add" Button under -Virtual Interfaces-
Make sure you leave it bridged, there is a bug in Broadcoms proprietary driver that causes problems with unbridged VAPs. Leaving it bridged as such will allow you to set up WPA security on the new WLAN.
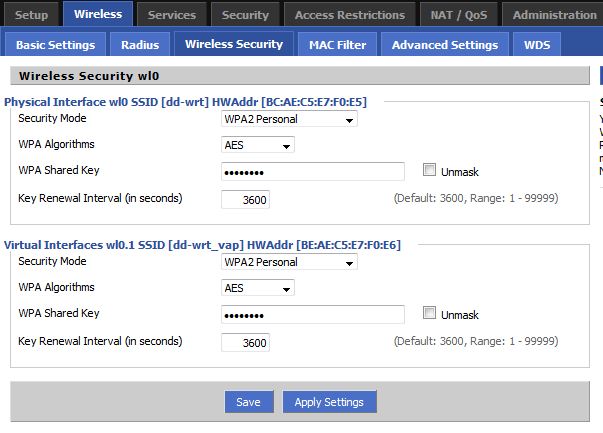
Secure the VAP. Go to Wireless -> Wireless Security and set up WPA.
Now we need to separate the two access points. Navigate to Setup -> Networking and click "Add" under "Create Bridge" You will see a new bridge populate the menu. Fill it it's network information (make sure that it is different than your main network) and apply settings. The router will reboot.
In the "Assign to Bridge" pane, click 'Add' to add a new assignment. Select 'your new bridge (br1) and VAP (wl0.1) from the drop down menu. You can leave STP enabled if you'd like. It will help if you set up routing loops on accident. Apply settings. The router will reboot. After the page refreshes the bridge assignments should look like the picture below.
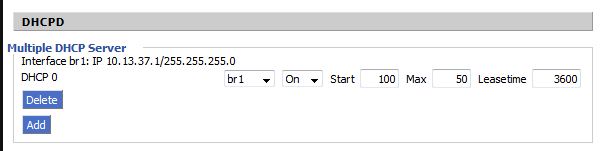
Down at the bottom of the same screen, in the DHCPd pane, click the add button. Once the page refreshes select the new bridge you created earlier and apply settings. The router will reboot.
Under Setup -> Basic Setup make sure the boxes for Use DNSMasq for DHCP and Use DNSMasq for DNS are checked. Save settings.
Then, navigate to Services -> Services and ensure that DNSMasq is enabled, Local DNS is disabled, and No DNS Rebind is Enabled. Enter the following into Additional DNSMasq Options: dhcp-option=br1,6, 8.8.8.8, 8.8.4.4
When you are finished it should look like the picture below. Apply settings.
[edit] Policy Based Routing
Now all we have left to do is set up our IP route maps so the router knows what to do with information coming in on the new VAP. You will not need to use iptables at all for this provided you set up OpenVPN correctly. The only exception to this is if you require port forwarding through your VPN tunnel. Then you will need to forward the interfaces to each other. If this is the case, add the following to the end of the firewall script below.
iptables -A FORWARD -i br1 -o $tun_name -j ACCEPT #Needed for port forwarding iptables -A FORWARD -i $tun_name -o br1 -j ACCEPT #Needed for port forwarding
A few notes before we start...
@netaddr is the network address of your VAP.
How to find your network address: I am not going to list out all possible network addresses for all possible subnets. If you are using a subnet address that is different than your standard 255.255.255.0, you should understand how subnetting works... and be able to find it yourself. For the rest of you, assuming you are using the above subnet for your network, your network address will be the first three octets of your bridge's ip address with a .0/24 at the end. Example: Your bridge IP address is 10.13.37.1. You trim the last octet, and add .0/24. This ip now becomes 10.13.37.0/24.
The device designation of your tunnel device set up by OpenVPN needs to at least start with the characters 'tun' for this script to work. For most people it will be named tun0 or tun1.
Go to Administration -> Commands and save the following as your startup script, and reboot your router.
sleep 45; tun_name=$(ifconfig | sed -n 's/.*\(tun[^ ]\).*/\1/p'); tun_addr=$(ifconfig $tun_name | sed -nr 's/.*P-t-P:([^ ]+) .*/\1/p'); ip rule add from '''@netaddr''' table 200; ip route add default via $tun_addr dev $tun_name table 200; ip route flush cache;
This script waits 45 seconds (enough time for the VPN tunnel to come up)... pulls the P-t-P address of your tunnel interface and the interface name and adds the proper entries to your routing table. Note that if the tunnel drops, the routes drop... and will not come back up until you restart your router or rerun the firewall script.
You should now be able to connect to both access points. Go to www.whatismyip.com on both and make sure that the IP addresses are different (They should be if you are connecting to a remote VPN).
This same method should work for PPTP VPNs as well, as long as you're NOT running PPPoE on your WAN. You'd just need to change one line in the script to make it work.
Change
tun_name=$(ifconfig | sed -n 's/.*\(tun[^ ]\).*/\1/p');
To:
tun_name=$(ifconfig | sed -n 's/.*\(ppp[^ ]\).*/\1/p');
Note: If you are running PPPoE and a PPTP VPN, manually set tun_name to the tunnel's interface name created by your PPTP VPN.